Key Benefits
-
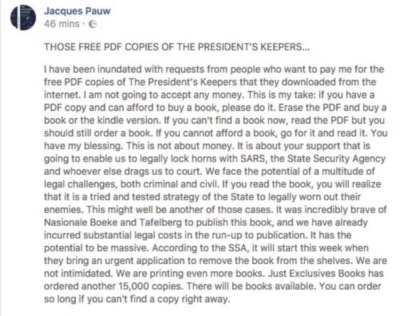
Deter leaks.
Potential leakers know that they can be traced. Each copy of a document contains a unique watermark directly associated with the authorized recipient.
-
Detect leaks anywhere online.
Custos’ blockchain-based tracking solution allows the breach to be detected rapidly, in the furthest corners of the web.
-
Identify leakers.
Once a leak is detected, Custos’ tracking system reveals the identity of the recipient whose copy was leaked.