Custos launched a new secure digital asset management platform that embodies the next generation of data security made possible by blockchain technology. Up to now, data breach prevention has only focussed on securing data storage and distribution, but not the user. This is the missing puzzle piece that Custos’ blockchain tech provides.
Traditional Data Security – Leaving the Back Door Unlocked
Data infrastructure has three components: storage, distribution, and the user. Both encryption (which secures storage) and access control (which secures distribution) have become ubiquitous in all industries.
Even so, the 2019 IBM Cost of Data Breach report found that the odds of experiencing a data breach is increasing for businesses – There’s a 29.6% chance of a company experiencing a data breach in the next 24 months today compared to only 22.6% in 2014.

The neglected component of data infrastructure is the user. The user is both the favored point of entry for malicious attack and directly causes 49% of data breaches through human error.
The key to securing the user-component of data infrastructure is to influence the incentives of the people interacting with your data.
A user with a strong enough incentive (or lack of a strong enough disincentive) will always manage to circumvent the other means of security. Take the film industry, for example – with no threat of being caught, users are happy to share VOD credentials, circumventing access control. Motivated pirates screengrab movies to circumvent encryption. In the film industry, the most sensitive and valuable data – pre-release movies – leak more than 20% of the time.
By simply adding a credible threat of detection to the user, data breaches are reduced to zero.

The Custos system secures the user by embedding unique Bitcoin bounties into all media that are distributed. If a user circumvents the access control and encryption protecting the media, anyone that sees the media where it shouldn’t be can claim the bounty. When the bounty is activated, the infringing user is identified. This threat of detection adds a strong disincentive to any user to maliciously leak data and gives them skin in the game, which reduces negligent leaks.
DAM good security
While Custos has solutions for film screener protection, education platform protection, and document protection, most enterprises in the knowledge economy manage a range of sensitive media types for various projects, including video, images, and documents. A digital asset management platform (DAM) allows for the presentation, distribution, and protection of multiple media types collected into projects.
Custos security is integrated into a leading open-source distribution platform to provide security from the ground up. All content is encrypted at rest, and granular access control means that content is shared on a need-to-access basis. On top of this, all videos, images, and documents that are distributed on the platform are embedded with the Custos blockchain watermark. All three components of the data infrastructure are secured.
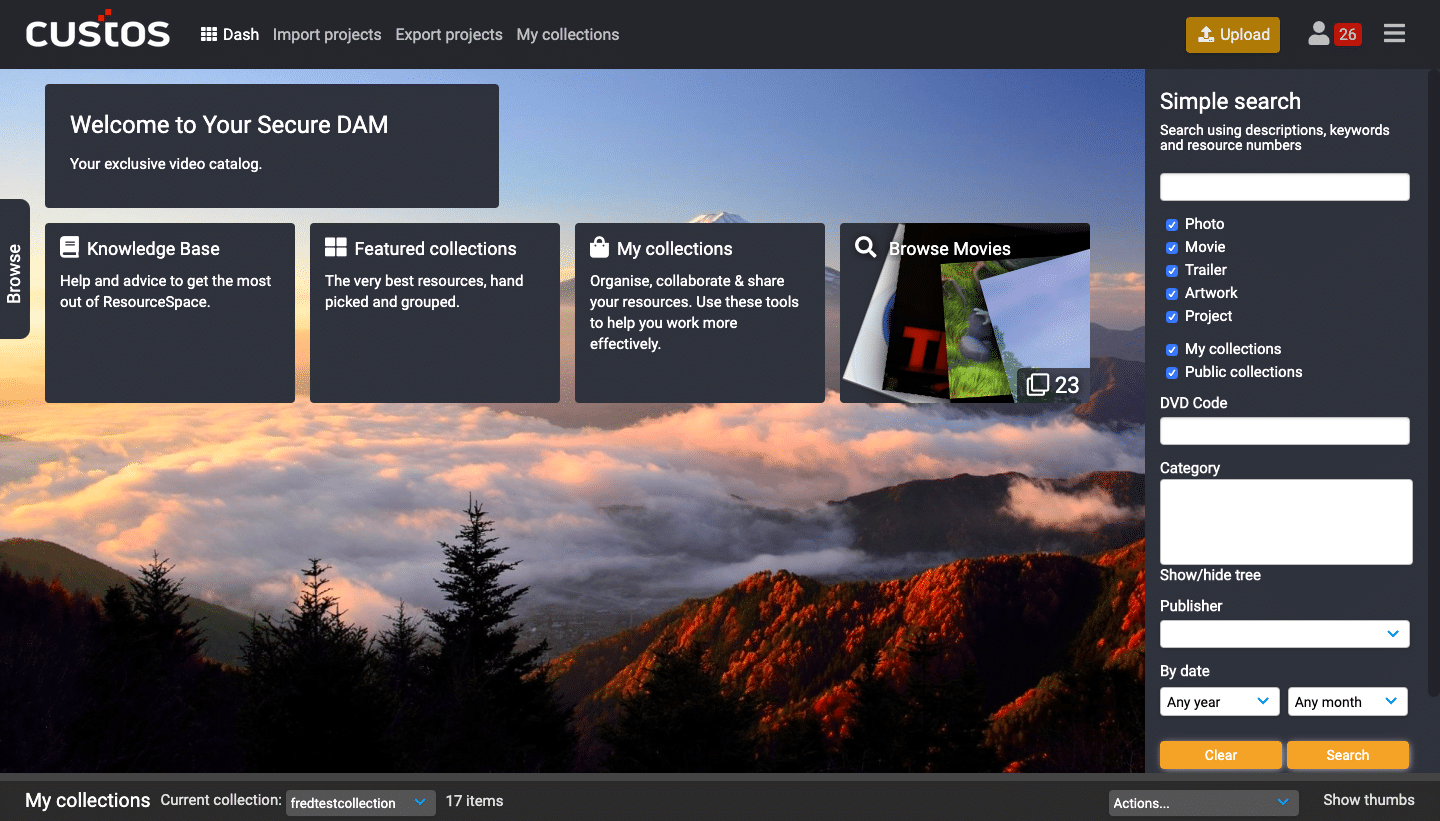
The Custos DAM is adaptable to all secure media distribution and collaboration.
Use Cases
Education
Educators can create courses, upload rich content, and securely share them with students. Students can view and download videos, documents, and images and submit assignments directly on the platform. Sensitive information is secured, and the reselling of costly content is stopped.
Product Development
Modern product development is a collaborative cross-team process. Custom workflows increase efficiency and ensure that everyone has access to all the content they need. Eliminate leaks of designs or product plans to competitors or the media.
Marketing Development
Images, copy, and designs can be managed and shared collaboratively on the platform without fear that anything will slip past embargoes.
Film Sales
Upload dailies, screeners, and full movies to the platform. The marketing team can add metadata, posters, and press releases. Press packs with screeners can securely be shared with journalists without the threat of piracy.
You can download the Custos Resources DAM pamphlet here. Interested to see how the Custos technology is being used? See our case studies here.


